Research
Share Knowledge
Brainstorm Ideas
Achieve More
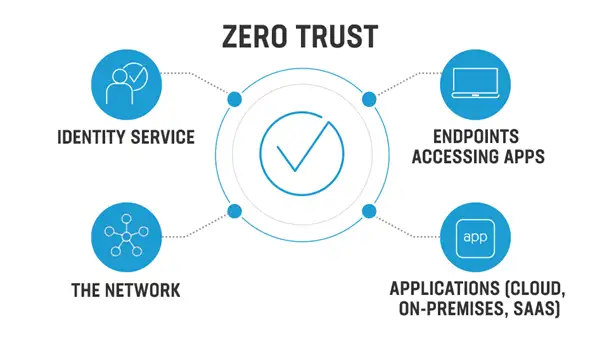
Cybersecurity is a major area of concern for enterprises across the globe. While enterprises across the globe are looking for ways to strengthen their cybersecurity posture, Zero Trust Architecture comes up as a reliable strategy, framework cum philosophy for enterprises to give them enhanced protection against matured cybersecurity threats especially in the context of 2023. Zero Trust is abbreviated as ZTNA and has demonstrated strong competence in securing businesses from a wide array of risks. The increased threat perception in 2023 is witnessing a surge in ZTNA implementation across industries.
Before understanding the character of ZTNA and its advantages at the organizational level, let us understand the threat posture looming ahead for CISOs in 2023.
Security and Data breach are the biggest risks for today’s businesses. A single data breach can lead to a million-dollar loss. The monetary value can go up since we have taken a rough figure for generic reference. Hefty security breaches can cause multiple financial disasters for companies arising out of penalties, lawsuits & compensations. On January 17th, hackers stole approximately $18 million worth of Bitcoin and $15 million worth of Ethereum.
Malware attacks have been reported from different corners of the world in 2022. Hence, it has been recognized as one of the principal cybersecurity threats. Zero Trust Architecture offers a significant amount of protection against malware attacks. Without Zero Trust Architecture, business assets would always be at risk of potential Malware Attacks along with Security & Data Breach.
Ransomware attacks have already resulted in significant monetary losses for businesses in 2022. Many businesses ended up paying hefty ransomware amounts to the attackers and some even did not report the attacks to law enforcement authorities. ZTNA offers a significant amount of protection against Ransomware attacks.
Email spoofing is a very common problem which puts enterprise data and client assets under a significant amount of risk. Spoofing is plain and simple forgery of identity by expert cybercriminals. Spoofing attacks are very common and come disguised making it very difficult to track and detect.
Phishing or identity theft is used by cybercriminals to steal money from individuals or business corporations. Phishing attacks have increased in the year 2022. Hence, ZTNA is an absolute necessity for enterprises to counter threats like phishing.
Zero Trust is based on the principle – ‘Never Trust! Always Verify!’
This step mandates strong verification of user identity, least access and thorough verification of user device integrity.
The application of ZTNA implies that the implicit trust factor is unavailable for applications and their individual components. They require continuous monitoring during the run time.
All important components of the infrastructure like server, router, switch, cloud, IoT etc must be addressed with Zero Trust Approach.
The threat surface of attack is minimized with the implementation of Zero Trust Architecture. Users, applications and infrastructure face a reduced threat margin due to the very framework of ZTNA.
Better authentication ensures that the threat level is minimized with each layer of interaction.
ZTNA restricts lateral movement across applications and only allows specific access to applications and platforms to an user.
Data exfiltration is limited significantly by ZTNA.
Internal and external security threats are minimized with the security wrapping of each workload and compute container to prevent data theft or unauthorized access.
The journey towards implementing successful Zero Trust Model within the framework of an enterprise can only be completed by a reliable Cybersecurity consultant. ITPN offers advisory, consulting, and wide range of services, products, and certified IT security professionals, with pioneering expertise and rare experience to help our client's safeguard their critical assets (Infrastructure, Data, Identity & Access Management, Applications, and other Assets) by identifying, protecting, managing and adequately responding to security threats and incidents.