Research
Share Knowledge
Brainstorm Ideas
Achieve More
A multi-tenant architecture accommodates separate virtual machines concurrently functioning on a shared physical server. One consequence is that multi-tenancy in a shared cloud environment becomes prey to security threats.
Most of these threats stem from one tenant's ability to execute arbitrary programs and/or access physical server components that may impact other tenants. Hence, to protect multi-tenant cloud instances, it is necessary to be able to monitor and control all activities carried out by all tenants. Likewise, it's essential for individual tenants to be able to audit all the potentially harmful non-privileged execute activity.
"Cloud strategies usually lag behind cloud use," says Kasey Panetta from Gartner. She also suggested that almost 90% of the organizations could find themselves regularly exposed to cyber threats by 2025 if they fail to implement a robust cloud security strategy.
The risks become manifold when considering multi-tenant cloud instances because they are exposed to:
With these risks looming, it's essential to be proactive in securing a multi-tenant environment.
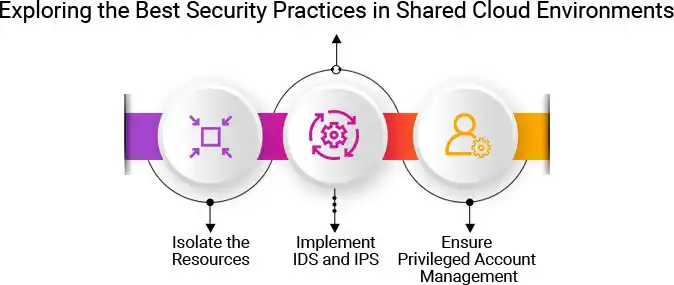
First things first, why isolate the resources? The answer lies in the ease of exploitation facilitated by the multi-tenant architecture itself. Consider this; attackers often monitor the network and practice brute force. A multi-tenant architecture only makes it easy for them to succeed in their endeavors by allowing residence in neighboring virtual machines. Such proximity paves the way for side-channel attacks.
Hence, resource isolation becomes imperative to tackle the noisy neighbor problem and keep the performance intact. Following are some of the core isolation strategies as suggested by AWS.
Another strategy that's highly recommended is the deployment of intrusion detection systems (IDS) and intrusion prevention systems (IPS). IDS can be used to detect possible system faults and malicious attempts. IPS, on the other hand, acts as a security guard at the entry points of a network.
As such, IDS can be employed in segregation, i.e., host-based IDS can be placed for internal monitoring of the use of resources. Through such monitoring, it can notify the administrator of any erroneous thread allocations. Alternatively, network-based IDS can be employed to detect unauthorized attempts at connecting to a network. In order to monitor the entire traffic, it can be used as a universal IDS.
While the employment of IDS and IPS is paramount, it doesn't imply that it's a comprehensive solution to the multi-tenant cloud security problem. Multi-tenancy isolation, as explained previously, still needs to be meticulously implemented in the deployment architecture.
Overall, it's crucial to manage the ecosystem via regular practices to prevent unauthorized attacks on shared cloud instances. For instance:
While multi-tenancy has multiple benefits, including cost-effectiveness, scalability, and elasticity, its inherently high risk of soundly imploding in the event of unauthorized attacks is a big concern for customers and cloud service providers alike.
We at ITPN understand that the security issues in a multi-tenant cloud can be exasperatingly complex. However, we also understand that they don't have to be. We design, implement, and manage solutions that can make your cloud more secure even (and especially) while upholding its performance.
For more information on securing multi-tenant cloud solutions, get in touch with us today.